NEXT COURSE DATE: MON 6TH - 10TH MAY 2024: COST ₦ 97,000.00
PRACTICAL ACCESS CONTROL INSTALLATION EIS LEVEL - 3 CERTIFICATE. DURATION: 5 DAYS.


For 3x Instalment Payments, Contact Us @ +234(0)8134466621 Or Send Email To info@eis-academy.com For Arrangements.
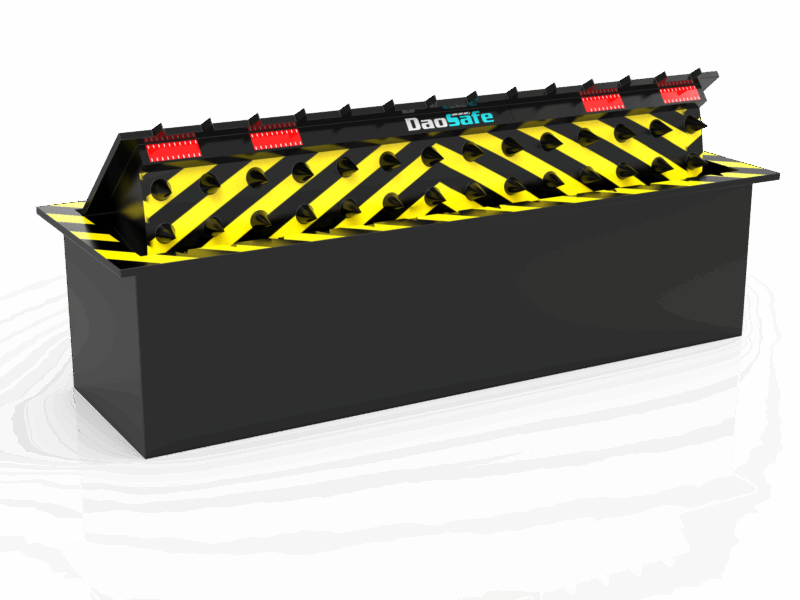
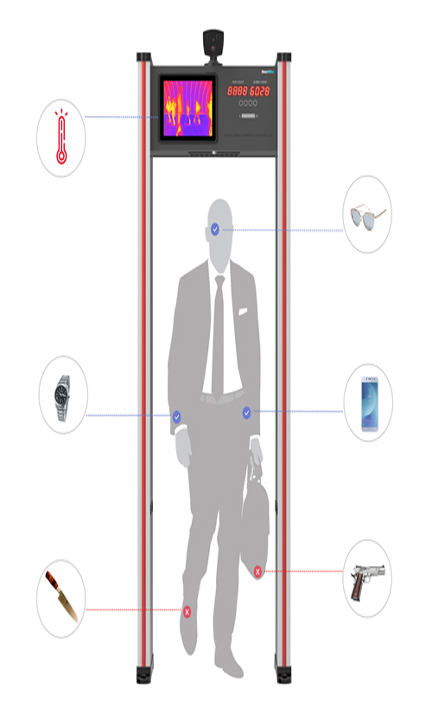
In todays world of technology disruption, Access Control has become most adopted smart security method to control movement of people, cars, granting access to the right people and denying access to passage to an unauthorised persons from a secured area or section of an environment. Access Control usage spans from airports to wharf, stadium, hospitals, schools, government houses, offices, industries, organisation etc. This comprehensive Hands-On-Practical Access Control course after successful completion will give you an in-depth knowledge of how to install different type of Access Control devises ranging from automatic door locks with card readers, PIN codes, face recognition and fingerprint, Automatic Gates etc. You will learn different types of Turnstiles, Speed Gate, Metal Detector, Access Controller, Barrier Gate, Security Bollards etc.
WHAT YOU WILL LEARN:
You will learn site surveying and system designs, the tactical skills to design, install, operate, repair, maintain and commission a fully networking access control
There are no prerequisites to attend this course, the course is specifically designed for those wishing to navigate their career to smart world of technology in Access Control.







COURSE PROGRAM:
- Introduction
- Objective Of Access Control
- Access Control Environmental Consideration
- Categories of Equipment
- Operational Requirements
- Access Control Alarm Monitoring Systems Integration
- Communications
- Power Requirements
- Costing Analysis
- Facial Recognition
- Fingerprint Recognition
- Hand/Finger Geometry Recognition
Physical Identity Access Control – PIAC
Barriers
Bollards
Turnstiles and Portals
Tokens and Cipher Systems
Identification Cards and Badges
Keycard Door Systems
Magnetic Stripe Cards
Contact Smart Card
Contactless Smart Card..
Wiegand Cards.
Key Fobs
Biometric Access Control Technologies Devices
Verification and Identification

For 3x Instalment Payments, Contact Us @ +234(0)8134466621 Or Send Email To info@eis-academy.com For Arrangements.



NEXT COURSE DATE: MON 6TH - 10TH MAY 2024: COST ₦ 97,000.00
ACCESS CONTROL IN BRIEF:
Access Control: Door locks, Automatic doors, Auto Gates, Auto Shutters, Barriers, Turnstiles.
Introduction:
In the fields of physical security and information security, access control (AC) is the selective restriction of access to a place or other resource.
The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.
Locks and login credentials are two analogous mechanisms of access control.
That makes the access control business big business, and something you can potentially make a great deal of profit from being involved in.
The access control industry is a huge industry that accommodates experts who are specialized in different fields, and innovations in both practice and technology are always occurring.
So, if you are looking towards starting a business in the security industry, there are several money spinning business opportunities that are available. Our aim is to provide you the training and skills that you need to start your own profitable security business.
Access Control Systems (Door Locks)
The term access control refers to the practice of restricting entrance to a property, a building, or a room to authorized persons.
Physical access control can be achieved by a human (a guard, bouncer, or receptionist), through mechanical means such as locks and keys, or through technological means such as access control systems like the mantrap. Within these environments, physical key management may also be employed as a means of further managing and monitoring access to mechanically keyed areas or access to certain small assets.
When a door is locked, only someone with a key can enter through the door, depending on how the lock is configured.
Mechanical locks and keys do not allow restriction of the key holder to specific times or dates. Mechanical locks and keys do not provide records of the key used on any specific door, and the keys can be easily copied or transferred to an unauthorized person. When a mechanical key is lost or the key holder is no longer authorized to use the protected area, the locks must be re-keyed.
Access Control System Operations
When a credential is presented to a reader, the reader sends the credential’s information, usually a number, to a control panel, a highly reliable processor. The control panel compares the credential’s number to an access control list, grants or denies the presented request, and sends a transaction log to a database. When access is denied based on the access control list, the door remains locked. If there is a match between the credential and the access control list, the control panel operates a relay that in turn unlocks the door. The control panel also ignores a door open signal to prevent an alarm. Often the reader provides feedback, such as a flashing red LED for an access denied and a flashing green LED for an access granted.
The above description illustrates a single factor transaction. Credentials can be passed around, thus subverting the access control list. For example, Alice has access rights to the server room, but Bob does not. Alice either gives Bob her credential, or Bob takes it; he now has access to the server room. To prevent this, two-factor authentication can be used. In a two-factor transaction, the presented credential and a second factor are needed for access to be granted; another factor can be a PIN, a second credential, operator intervention, or a biometric input.
There are three types (factors) of authenticating information:
- Something the user knows, e.g. a password, pass-phrase or PIN
- Something the user has, such as smart card or a key fob
- Something the user is, such as fingerprint, verified by biometric measurement
Passwords are a common means of verifying a user’s identity before access is given to information systems. In addition, a fourth factor of authentication is now recognized: someone you know, whereby another person who knows you can provide a human element of authentication in situations where systems have been set up to allow for such scenarios.
For example, a user may have their password, but have forgotten their smart card. In such a scenario, if the user is known to designated cohorts, the cohorts may provide their smart card and password, in combination with the extant factor of the user in question, and thus provide two factors for the user with the missing credential, giving three factors overall to allow access
Access Control Systems (Automatic Doors, Gates & Shutters)
Electronic access control uses computers to solve the limitations of mechanical locks and keys. A wide range of credentials can be used to replace mechanical keys.
The electronic access control system grants access based on the credential presented. When access is granted, the door is unlocked for a predetermined time and the transaction is recorded. When access is refused, the door remains locked and the attempted access is recorded.
The system will also monitor the door and alarm if the door is forced open or held open too long after being unlocked.
The same method can also be applied to gates, shutters, barriers and turnstiles.
How can I make Access Control Systems my business?
Access Control Systems can be a profitable business, whether you are thinking about starting a fully-fledged security company, or going into the installation of Access Control Systems and other security systems.
It’s a business that you can kick start after undergoing some training such as the course we offer.
This is also a business that an entrepreneur can launch with little start–up capital and grow organically.
Future growth
There is no doubt that Access Control Systems are a growth businesses.
Businesses and public sector organizations as well as private occupancies are all potential customers.
You can provide them that assurance of safety, and that is priceless.
Few Training Pictures From Our Centre







